- Home
-
SERVICES
Services offered by RM
-
SPECIALITIES
Major specialities
- WHY RM?
- SOFTWARES
- COMPLIANCES
- ABOUT US
Please fill out the form below if you have a plan or project in mind that you'd like to share with us.
Happy Clients
Projects Delivered
Skilled Employees
Support Available
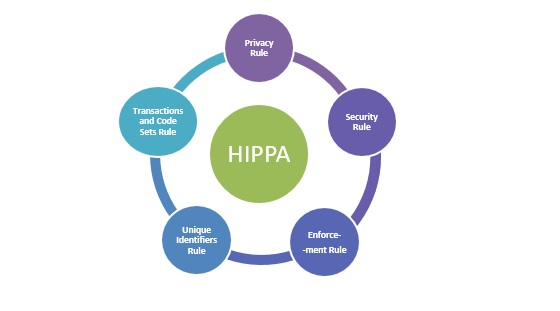
The Health Insurance Portability and Accountability Act of 1996 is known by the acronym HIPAA. The phrase is also widely used to refer to the numerous regulations that have been issued under that law since its passage in 1996. The HIPAA rules, which include the widely reported Patient Privacy and Security rules, are a set of laws that show how the US government is attempting to regulate the healthcare sector.
Any organization that maintains or transmits patient data is required by HIPAA to implement enterprise-wide measures to comply with its strict privacy, security, and transactional requirements. In essence, HIPAA mandates that healthcare organizations make sure to safeguard patient privacy rights and personal health information.
Under HIPAA’s Privacy Rule, RM Healthcare is a Business Associate. A Business Associate (BA) is any person(s) or entity, which performs a function or activity on behalf of a Covered Entity (CE) and involves the use or disclosure of Protected Health Information (PHI). At RM Healthcare, we are very serious about compliances. We have undertaken various steps and designed our process to ensure we are fully compliant.
Our entire network is very secure. All clients' office records are temporarily stored behind a secure firewall before deletion and all electronic claims are securely encrypted for transmission. Your privacy and security are given the highest priority at RM Healthcare. RM Healthcare ensures that all the changes and updates made by HIPAA are properly and correctly communicated amongst the team to ensure highest standards of security and confidentiality.
As an enterprise RM Healthcare is very vigilant about Information security and data safety. We have implemented several processes to ensure network security and data protection.
Network security is a way of making sure the security of an information technology system, including all network activity. It encompasses both computers and servers. Internet access is controlled by effective network protection, which identifies and stops a variety of dangers from propagating or accessing the system.
RM Healthcare make Confidentiality and Non-Disclosure Agreements as legally mandatory formal agreements. To ensure information is fully protected these documents are signed with our employees, and third party vendors (like IT Suppliers) who access our clients’ information.
Gateway security, anti-spyware, intrusion prevention system, application control service, and content/URL filtering features are implemented with Network Security Appliance. Managed Switches are used to create Multiple VLAN's with defined security policies.
Multifactor authentication using biometric technology is implemented to manage entry access to RM Healthcare premises. 24/7 Physical surveillance system installed to monitor transition of human and other resource.
Email Access enabled to leadership team and executives to communicate with clients and internal team. Security rules are configured in email server; attachment policy is ensuring denial of unapproved attachment types found in mails and send mail rules are ensuring the access restriction to send mail to personal email domain IDs and other unapproved email domain IDs. Spam filter implemented at mail server to safe guard mail information from malware / virus.
Data security is the practice of protecting digital information from unauthorized access, corruption, or theft throughout its entire lifecycle.
Network security is any activity designed to protect the usability and integrity of your network and data. It includes both hardware and software
Physical security is the protection of personnel, hardware, software, networks and data from physical actions and events that could cause serious loss
Email security solutions are designed to protect against phishing attacks and other email-borne attack vectors, protecting email accounts from external threats.